Set Up SAML Based SSO
Security Assertion Markup Language (SAML) is an XML standard for exchanging authentication/authorization data between parties, to specify, an identity provider and a service provider. Using the SAML model, Opsgenie acts as the service provider and supports SAML 2.0 based Single Sign-On to authenticate users through different identity providers. You can take a glance at our identity provider partners, the requirements to enable Single Sign-On for authentication and how you can configure and use our Single Sign-On solution, you can refer here. You can enable our Single Sign-On solution using any identity provider, even ones that are currently not one of our partners.
Setup Instructions for SAML 2.0 Based SSO Integration:
Order of the setup instructions may vary by the identity provider. Please do not hesitate tocontact us if you encounter any problem while setting up SSO integration with your identity provider or for any further assistance.
- Open SSO Settings Page and switch to SAML segment as identity provider.
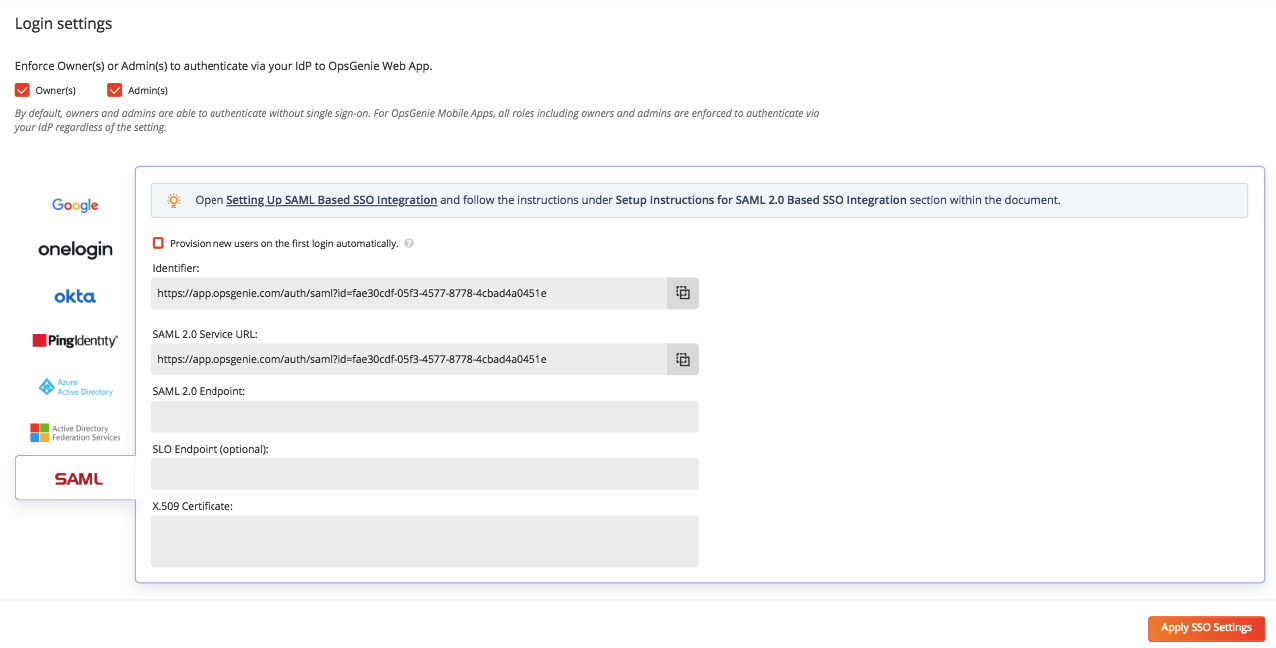
- If your identity provider needs you to specify SAML Identifier for Opsgenie (It may also be referred as Audience or Target URL), use the value of the field Identifier.
- Use the value of the field SAML 2.0 Service URL as the Consumer URL (It may also be referred as SSO Endpoint or Recipient URL) for your identity provider.
- Retrieve Single Sign-On (SSO) Endpoint from your identity provider and paste this URL into SAML 2.0 Endpoint field.
- If your identity provider supports Single Logout (SLO), retrieve SLO Endpoint from your identity provider and paste this URL into SLO Endpoint field. This field is optional.
- Export your X.509 certificate, copy its content and paste this certificate value into X.509 Certificate field.
- Check Enable Single Sign-on field and click Apply SSO Changes
- Now users in the directory of your identity provider can login with Opsgenie via SSO using their directory credentials.
Opsgenie Endpoints
SAML Identifier/Audience/Target URL): Copy Identifier field from from your SSO settings of Opsgenie account.
Assertion Consumer URL / Opsgenie SSO Endpoint: https://app.opsgenie.com/auth/saml?id=<saml_id> where <saml_id> is unique per Opsgenie account.
These endpoints can be found on SSO page.
Opsgenie SAML Attributes
Opsgenie uses the following attributes & values while performing an authentication request to your identity provider:
Version: 2.0
AssertionConsumerServiceURL: https://app.opsgenie.com/auth/saml?id=<saml_id> (which is the Opsgenie SSO Endpoint)
Issuer: https://app.opsgenie.com/auth/saml or https://app.opsgenie.com/auth/saml?id=<saml_id> (which is the Opsgenie SAML Identifier) See your Opsgenie settings page.
NameIDPolicy:
- Format:
urn:oasis:names:tc:SAML:1.1:nameid-format:emailAddress - AllowCreate:
true
ProtocolBinding: urn:oasis:names:tc:SAML:2.0:bindings:HTTP-POST
Validations & Enforcements by Opsgenie using SAML
The only supported SAML version is 2.0
Name ID format is expected to be: urn:oasis:names:tc:SAML:1.1:nameid-format:emailAddress.
(Name ID which is also e-mail address of the user on your identity provider should be equal to Opsgenie user name of the user.)
An encryption certificate for claims should not be used.
SAMLRequest that Opsgenie Sends to Your IdP
<samlp:AuthnRequest
xmlns="urn:oasis:names:tc:SAML:2.0:metadata"
ID="_950adbf4-34fe-492b-91d9-b6418feb56eb"
Version="2.0" IssueInstant="2017-08-17T15:29:46Z"
AssertionConsumerServiceURL="https://app.opsgenie.com/auth/saml?id=SSO_ID"
ProtocolBinding="urn:oasis:names:tc:SAML:2.0:bindings:HTTP-POST" xmlns:samlp="urn:oasis:names:tc:SAML:2.0:protocol">
<Issuer xmlns="urn:oasis:names:tc:SAML:2.0:assertion">https://app.opsgenie.com/auth/saml</Issuer>
<samlp:NameIDPolicy Format="urn:oasis:names:tc:SAML:1.1:nameid-format:emailAddress" AllowCreate="true"/>
</samlp:AuthnRequest>
* The XML content above is the SAML request that Opsgenie gives to your IdP as Base 64 Encoded, Deflated and URL encoded according to SAMLv2.0 protocol. Your identity provider should be able to process this content.
- SSO_ID represents the unique identifier that Opsgenie generates and provides within SSO page. So, the following is an example AssertionConsumerServiceURL value:
https://app.opsgenie.com/auth/saml?id=53bd8491-ef30-4d3e-92ed-bec8f09188bc
Example SAMLResponse that Opsgenie Receives from Your IdP
<samlp:Response
xmlns:saml="urn:oasis:names:tc:SAML:2.0:assertion"
xmlns:samlp="urn:oasis:names:tc:SAML:2.0:protocol"
ID="Ref34f454eda06982d99753378d61a2c21d160514"
Version="2.0"
IssueInstant="2017-08-16T13:41:51Z"
Destination="https://app.opsgenie.com/auth/saml"
InResponseTo="_5b7d882a-c1b0-4c6a-99e7-6c62ec267059">
<saml:Issuer>https://app.onelogin.com/saml/metadata/692790</saml:Issuer>
<samlp:Status>
<samlp:StatusCode Value="urn:oasis:names:tc:SAML:2.0:status:Success" />
</samlp:Status>
<saml:Assertion
xmlns:saml="urn:oasis:names:tc:SAML:2.0:assertion"
xmlns:xs="http://www.w3.org/2001/XMLSchema"
xmlns:xsi="http://www.w3.org/2001/XMLSchema-instance" Version="2.0" ID="pfxb2557bd0-0985-4bee-e1b7-be41c3f3f8c0" IssueInstant="2017-08-16T13:41:51Z">
<saml:Issuer>https://app.onelogin.com/saml/metadata/692790</saml:Issuer>
<ds:Signature xmlns:ds="http://www.w3.org/2000/09/xmldsig#">
<ds:SignedInfo>
<ds:CanonicalizationMethod Algorithm="http://www.w3.org/2001/10/xml-exc-c14n#" />
<ds:SignatureMethod Algorithm="http://www.w3.org/2000/09/xmldsig#rsa-sha1" />
<ds:Reference URI="#pfxb2557bd0-0985-4bee-e1b7-be41c3f3f8c0">
<ds:Transforms>
<ds:Transform Algorithm="http://www.w3.org/2000/09/xmldsig#enveloped-signature" />
<ds:Transform Algorithm="http://www.w3.org/2001/10/xml-exc-c14n#" />
</ds:Transforms>
<ds:DigestMethod Algorithm="http://www.w3.org/2000/09/xmldsig#sha1" />
<ds:DigestValue>NCvDMpITKYjYhSP0xHVFJNOUjpg=</ds:DigestValue>
</ds:Reference>
</ds:SignedInfo>
<ds:SignatureValue>HIQ/cvi6G6NoKCbDPTk9JugLhdGG3/VGGXGfS870M6aVOX09CTo9CCjZsdjmE7V8Tzf6GznR2B1cSBAvSVuVvMNqyrae6MxE+JIaCzyyKwhVmDEJyoWYXNK9VL8Kkfy4TROccW3D8eP6RKdC81TG1pUpqFWg3qczPLWdAEEAnBzfHDsGYg4x4KBCGDrx5YQsuV/qTi625tCJbUBezAfE9yut9D1GrHq5R2Sx+Sg07beqDlmHHRlUD4PEDjIQuHW5qfAabLit89JOsAdBrb2YkL6mYB3IhyuwQqVSZAIcYZlMnWHRMDnzg0axK4AwXpfs5xzokY3cG8aSIG5ylGs2nQ==</ds:SignatureValue>
<ds:KeyInfo>
<ds:X509Data>
<ds:X509Certificate>MIIEGjCCAwKgAwIBAgIUCzEy6NwCyLnG97HMVhLgzAZ9gy4wDQYJKoZIhvcNAQEFBQAwWTELMAkGA1UEBhMCVVMxETAPBgNVBAoMCE9wc0dlbmllMRUwEwYDVQQLDAxPbmVMb2dpbiBJZFAxIDAeBgNVBAMMF09uZUxvZ2luIEFjY291bnQgMTEyMzQ2MB4XDTE3MDgxNTEyNDMzOVoXDTIyMDgxNjEyNDMzOVowWTELMAkGA1UEBhMCVVMxETAPBgNVBAoMCE9wc0dlbmllMRUwEwYDVQQLDAxPbmVMb2dpbiBJZFAxIDAeBgNVBAMMF09uZUxvZ2luIEFjY291bnQgMTEyMzQ2MIIBIjANBgkqhkiG9w0BAQEFAAOCAQ8AMIIBCgKCAQEAvL5F9mMqveYJxUCk9yjGkg86FXinV6R70l2+nU5qZ+pOUoyzkeYziCcpgKKVPMGo5XUkkFcM5/BoLQB/t2XcRuBrGRIzKGzoushHHTVophVdQL2T6PvgXppr8TDMQ8YgvTf1mRxWlPxWVxR7QEZd3e+AKXyUZHTHEeay9UcPcRl9jvEp5MUZ0Gu3OjHVWoL4Vh1OMU+QKYXSk7zmdZ4/yRKq3mGJ8g9QLzRPvA39GRUXX4Qi34sjrRCK3A4bomylJPPU4gJKg0beFJmQJfAKQNHyvh43TF8Ry0trLsyJznkixxY6+q5EUeXc21B71XaVRpxKTRgjLIMkPtrlxr1YzwIDAQABo4HZMIHWMAwGA1UdEwEB/wQCMAAwHQYDVR0OBBYEFGc92CPSudOTjh2a/npNa/xeHOJFMIGWBgNVHSMEgY4wgYuAFGc92CPSudOTjh2a/npNa/xeHOJFoV2kWzBZMQswCQYDVQQGEwJVUzERMA8GA1UECgwIT3BzR2VuaWUxFTATBgNVBAsMDE9uZUxvZ2luIElkUDEgMB4GA1UEAwwXT25lTG9naW4gQWNjb3VudCAxMTIzNDaCFAsxMujcAsi5xvexzFYS4MwGfYMuMA4GA1UdDwEB/wQEAwIHgDANBgkqhkiG9w0BAQUFAAOCAQEAkdAjPRq5J7+RU3BBs2INT3SG/KMCJ+W/p5xHgkdQYuuucoBFVysUBN2x+66Njn/3bqsAgq2966sRJLOeaXBjtAcwHSOfu05LIGHxvfx8ZURHFF2U9+TupVXPf00Nza9BQ62w0jSPeo7+uvdm2iZnKdi1vHbhnjVzwT1+hDWXCBbN9SCxs+1ah6wF6IETXg84MSEB3ET2fM8PhNHdRjd78AHWqeJuFXpmkaXc8FnF3f8LDZF5w5p724e+5UAc75gSlknbUY5lnDzcp1zJHRvgMm+Kf8aAPWoZRyvAK2/O68navBLFrOiP9yqqowJWboMGJDKRpOPE0J48i2yTrRXT5g==</ds:X509Certificate>
</ds:X509Data>
</ds:KeyInfo>
</ds:Signature>
<saml:Subject>
<saml:NameID Format="urn:oasis:names:tc:SAML:1.1:nameid-format:emailAddress">USER_LOGIN_E_MAIL_ADDRESS</saml:NameID>
<saml:SubjectConfirmation Method="urn:oasis:names:tc:SAML:2.0:cm:bearer">
<saml:SubjectConfirmationData NotOnOrAfter="2017-08-16T13:44:51Z" Recipient="https://app.opsgenie.com/auth/saml" InResponseTo="_5b7d882a-c1b0-4c6a-99e7-6c62ec267059" />
</saml:SubjectConfirmation>
</saml:Subject>
<saml:Conditions NotBefore="2017-08-16T13:38:51Z" NotOnOrAfter="2017-08-16T13:44:51Z">
<saml:AudienceRestriction>
<saml:Audience>https://app.opsgenie.com/auth/saml</saml:Audience>
</saml:AudienceRestriction>
</saml:Conditions>
</saml:Assertion>
</samlp:Response>
USER_LOGIN_E_MAIL_ADDRESS is the login e-mail address (user name) of the authenticating user.
References
Assertions and Protocols for the OASIS Security Assertion Markup Language (SAML) V2.0
Updated 10 months ago
